For every major cybersecurity vulnerability that Ron Brash, MCompSc 17, successfully publicizes, he estimates that 10 to 12 are swept under the rug.
Named among the Top 40 Engineering leaders for 2020, Brash is vice-president of technical research and integrations at aDolus Technologies. The Victoria, B.C.-based cybersecurity firm specializes in industrial control software validation and vulnerability management, and tests products for large security vendors.
Yet unfortunately, their findings are sometimes ignored, Brash says. Because of the high cost of addressing vulnerabilities, some knowingly push out substandard technologies, offloading the burden onto the people who end up using them.
This can affect many critical domains, says Brash, “from vaccines to electricity to the water in our cities.” He explains the problem lies in the honour-based “best-effort” system, which relies on companies to report issues with their own products.
Brash is currently embroiled with a utility company over a device that delivers municipal water and oil and gas in many parts of the world. After two years of his team’s findings being ignored, Brash has brought their concerns all the way to the U.S. Department of Homeland Security.
Despite obstacles, Brash also scores big wins. In 2021, he discovered several vulnerabilities in General Electric’s power grid that were promptly addressed in a U.S. Government Cybersecurity and Infrastructure Security Agency advisory. And in early 2022, he identified security issues in the same power grid’s ABB protocol gateway interface and Bently Nevada Vibration Monitoring System, which have been resolved.
Stumping the world’s best
Brash is a frequent presenter at cybersecurity summits and conferences. At the 2019 S4 Industrial Control Systems conference, among the most advanced cybersecurity events in the world, Brash concocted a nearly insurmountable challenge for attendees.
He started by acquiring and anonymizing two colossal datasets, one from a mine and one from a trans-American pipeline, then programmed cyberattacks into it. In theory, products brought by conference goers — which they had spent months developing for this very purpose — should have honed right in on the attacks and rectified them. In reality? “Most products failed miserably," says Brash.
“The products had to understand where the attacks were happening and they couldn’t do it." While he acknowledges it was a particularly hard problem to solve, Brash says it’s close to what “someone with sophisticated means would’ve done,” alluding to cyberattacks from hostile nations.
He adds that this just shows the due diligence required by companies or governments when considering a cybersecurity product. “They can’t just trust the claims of vendors.”
From whiz kid to master’s in computer science
Originally from Tofino, B.C., Brash spent many rainy days indoors as a child, playing with his parents’ computer. He found he was good at hacking into systems, and eventually got involved in the “darker-arts” of computer science: learning to tamper with hardware to reload Starbucks gift cards and clone driver’s licenses. “I did it successfully,” he says. “It was easy at the time.”
Brash never used his skill to steal anyone’s identity or score a free blended drink. Instead, he leveraged it for good, eventually using those skills to locate vulnerabilities in critical infrastructure technology and protect it from cyberattacks.
When he arrived at Concordia in 2014 to complete a Master of Computer Science, it was to formalize knowledge he already had, he says, “lending him credibility for very prestigious audiences.” He notes his degree influenced how he approaches research and the way he manipulates data.
With the experience he got from Concordia, Brash was able to run a successful technology consultancy and expand his network. He says his investment in education generated substantial long-term rewards, and recommends prospective students treat education as an investment in achieving specific targets. “They must hold themselves accountable for their completion.”

 Ron Brash, MCompSc 17, is the vice-president of technical research and integrations at aDolus technologies
Ron Brash, MCompSc 17, is the vice-president of technical research and integrations at aDolus technologies
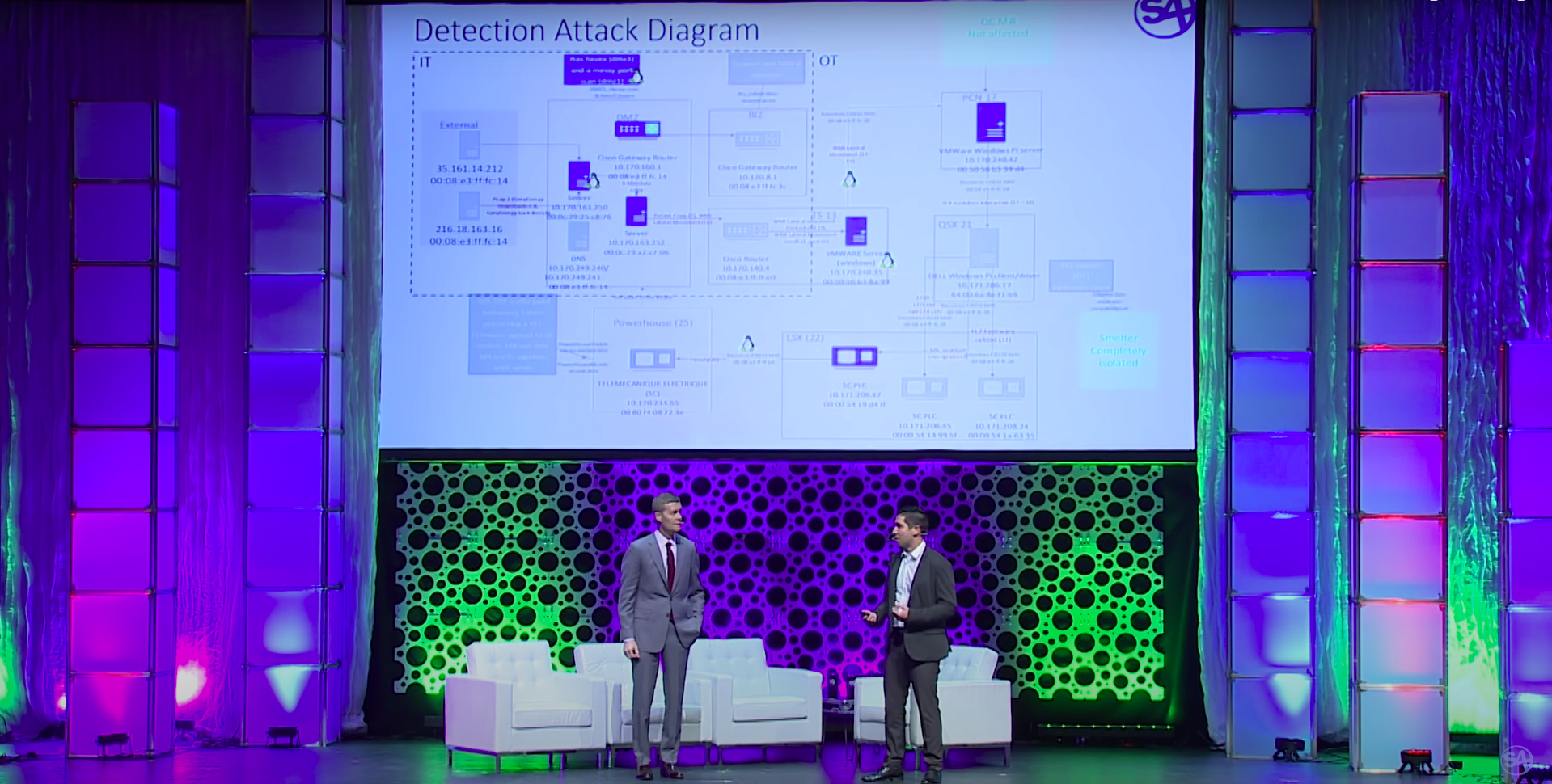 Ron Brash presenting at the 2019 S4 Industrial Control Systems Conference.
Ron Brash presenting at the 2019 S4 Industrial Control Systems Conference.