Concordia researcher looks to create an added layer of protection for cloud-based technologies

Smartphones. Smart watches. Smart homes. As the scope of fifth-generation technologies expands, so too does the infrastructure to support it. But as network applications move from physical to more agile and scalable virtual platforms, new threats and vulnerabilities arise.
The research of Azadeh Tabiban, PhD candidate at the Concordia Institute for Information Systems Engineering, focuses on making virtual environments more transparent and accountable. She is particularly interested in cybersecurity as it relates to cloud and network function virtualization (NFV) technologies.
Our day-to-day lives increasingly depend on the reliable operation of cloud services
How does this specific image relate to your research at Concordia?
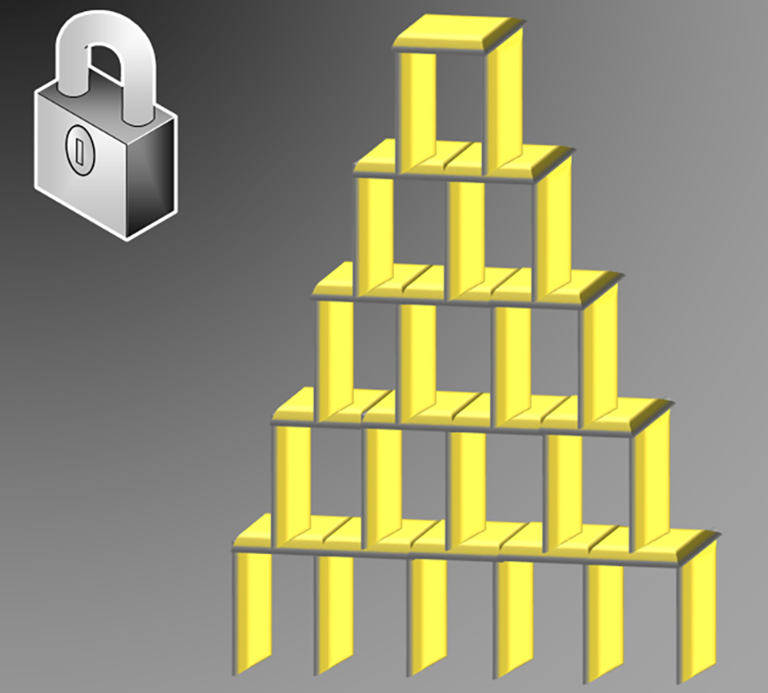
Azadeh Tabiban: The problem we deal with in NFV environments is analogous to what we have in a domino tower and its reliance on the right placement of each domino.
NFV technology brings a high vertical and horizontal complexity. In an NFV environment, a large number of components are chained together horizontally to fulfil end-to-end network services. Also, NFV is deployed in a multilayer architecture and thus the functionality of the whole system relies on the robustness of all layers in the NFV stack.
What is the hoped-for result of your project?
AT: NFV enables software-based network applications — for example, firewalls, intrusion detection systems, etc. — to run on virtual machines. They were traditionally implemented using dedicated and proprietary hardware middleboxes.
This allows more scalable and agile network services to be updated continuously with no interruption to customers, unlike their traditional counterparts.
However, relying on virtual environments for network functionalities introduces new security threats and vulnerabilities. For instance, security protection failures at virtual resources threaten the security of network functions and can be very difficult to discover.
Therefore, the main hoped-for result of my research would be a scalable framework for delivering an increased interpretability of the alert information collected from the NFV stack. I believe this would represent a significant step forward for more effective security solutions in NFV.
What impact could you see it having on people’s lives?
AT: Our societies are moving fast toward 5G and the Internet of Things (IoT). Our day-to-day lives increasingly depend on the reliable operation of cloud services and telecommunication infrastructures. Those services and infrastructures will now run on top of NFV.
My research has the potential of generating real-life impact in terms of providing an added layer of security protection over such services and infrastructures. It could also help to enable wider adoption of NFV as a cost-effective solution and thus provide significant financial and ethical benefits to our societies.
What are some of the major challenges you face in your research?
AT: First of all, as NFV is very new, a major challenge is the learning curve. However, I also see this as a great opportunity since there is more chance to make novel and significant contributions in such an emerging area. Technically, we face many interesting challenges in terms of scalability and efficiency, due to the size and agility of NFV environments.
What first inspired you to study this subject?
AT: My initial interest in cybersecurity, and NFV security in particular, was sparked by its impact on people’s daily lives. We keep hearing about identity thefts, smart home cyberattacks or unauthorized access to user habits information by advertisement companies or even for personal revenge purposes. These can mean serious threats on regular citizens’ lives. And they can be further exacerbated by higher attack surfaces and complexity introduced by NFV platforms and their interactions with smart devices continuously collecting sensitive information.
Cybersecurity also fascinated me during my master’s studies from the technical point of view, which further encouraged me to do research on it. There is a commonly used analogy between cybersecurity and building a castle — you need to be cautious about the slightest cracks. It is amazingly challenging to take the system you are studying in its entirety, attack it from every angle to find the cracks and then find a solution. Sometimes this requires demolishing the walls and rebuilding something entirely new.
What advice would you give interested students looking to get involved in this line of research?
AT: NFV security is a growing research area with real impacts on the advancement and secure deployment of 5G and IoT technologies. Researchers from different backgrounds in computer or electrical engineering have a great opportunity to conduct effective research addressing security challenges in different aspects of NFV.
To me, the best way to stay self-motivated in this kind of research is to remind yourself about the big picture, how this research fits into it and the potential for eventual success.
What do you like best about being at Concordia?
AT: Concordia has a very strong cybersecurity research group. Furthermore, we have a close and successful collaboration with industrial experts from Ericsson. This provides a great opportunity to learn about research problems and practical solutions for real-world systems and applications.
Also, Concordia has a multicultural and friendly community. By being part of it, one can enjoy interacting with and learning from people with different ways of thinking.
Over the past two years that I have been doing research on cloud and NFV security, I got involved in several industry-related research projects and co-authored a book on cloud security auditing. This would never be possible without the support of my advisor, Lingyu Wang, and the effective research team collaboration at Concordia.
Azadeh Tabiban’s research was supported by Ericsson, the Natural Sciences and Engineering Research Council of Canada and PROMPT-Québec.
Find out more about the Concordia Institute for Information Systems Engineering.


